CMMC Certification Explained: A Practical Guide for Defense Contractors
- Mar 17
- 12 min read
What makes CMMC different from prior cybersecurity mandates is enforcement. Organizations are no longer allowed to self-assert compliance and move on. They must prove, through assessment, that security controls are implemented, followed, and sustained.
This page is designed for organizations that already know CMMC matters and want practical clarity. We focus on how CMMC plays out in real environments, what organizations get wrong, and what to expect if certification is the goal.
What Is CMMC and Why It Exists
CMMC is a cybersecurity framework developed by the Department of Defense (DoD) to improve the protection of sensitive government information across the defense supply chain. Its creation reflects a growing recognition that cybersecurity weaknesses at any point in the supply chain can create outsized risk, even when the primary contractor has strong controls in place.
Historically, the DoD relied on self-attestation to enforce cybersecurity requirements. Contractors were expected to align with standards such as NIST SP 800-171 and to attest that required safeguards were implemented. While these requirements established an important baseline, enforcement was inconsistent, and verification was limited. As a result, cybersecurity maturity varied widely across organizations handling similar types of sensitive information.
Over time, the DoD observed that adversaries were increasingly targeting smaller contractors and suppliers as a way to gain indirect access to sensitive data. These organizations often lack the resources, structure, or oversight needed to maintain consistent security practices. CMMC was created in response to this reality, with the goal of raising the overall cybersecurity baseline across the Defense Industrial Base.
Rather than focusing solely on individual technical controls, CMMC emphasizes maturity and consistency. It introduces defined levels of cybersecurity capability and ties those levels to formal assessment requirements. Organizations handling Federal Contract Information (FCI) or Controlled Unclassified Information (CUI) must now demonstrate that their security practices are not only documented but actively followed and maintained as part of day-to-day operations.
Oversight of the CMMC ecosystem, including assessor accreditation and training, is managed by the Cyber AB. This governance structure is designed to promote consistency across assessments and reduce variability in how requirements are interpreted and evaluated.
Who Needs to Comply With CMMC
CMMC compliance applies to a broad range of organizations that do business with the Department of Defense. This includes prime contractors, subcontractors, suppliers, and service providers. The determining factor is not organizational size or revenue, but whether an organization handles FCI or CUI as part of contract performance.
We regularly see organizations underestimate their exposure because they define scope based on intention rather than actual behavior. In one recent engagement with a 60-person manufacturer, leadership was confident that CUI was confined to a single ERP environment. But once we began scoping interviews and artifact review, a different picture emerged. Engineers were emailing controlled drawings through personal Gmail accounts. That single discovery expanded their compliance scope across multiple systems and users and materially changed their remediation plan.
One of the most common misconceptions surrounding CMMC is that it applies only to prime contractors. In reality, cybersecurity requirements frequently flow down the supply chain. Subcontractors that support DoD contracts may be required to meet CMMC requirements even if they never contract directly with the government. If sensitive data touches their environment in any form, CMMC may apply.
This flow-down dynamic introduces significant risk for organizations that assume they are out of scope. Many companies discover late in the process that CUI exists in shared systems, cloud collaboration platforms, or third-party tools that were not initially considered. By the time this is identified, compliance timelines may already be compressed.
CMMC also affects organizations differently depending on their role in the supply chain. A manufacturer producing components for a defense system may face different scoping considerations than a professional services firm providing engineering or IT support. Understanding where data flows, who has access to it, and how it is protected is essential for determining which CMMC level applies.
Cyberleaf addresses these scoping challenges and flow-down considerations in more detail in What Is CMMC and Who Needs to Comply?, which explores common scenarios where organizations underestimate their compliance obligations.
Understanding the CMMC Framework
CMMC is designed as a maturity-based framework. Rather than applying a single set of requirements to every organization, it aligns cybersecurity expectations with the sensitivity of the data being handled and the potential impact of a compromise. This approach allows the DoD to apply stronger requirements where risk is higher, while avoiding unnecessary burden where exposure is limited.
At its core, the framework is structured around defined levels, each one representing a different degree of cybersecurity, maturity and rigor. As organizations move up the levels, expectations increase in terms of technical controls, documentation, process maturity, and assessment requirements.
Understanding the CMMC Levels
CMMC levels are designed to align security requirements with the type of information an organization handles. Each level builds on the previous one, adding depth and rigor as risk increases. While the framework has evolved over time, the intent remains consistent: ensure that organizations protecting sensitive defense information meet appropriate, verifiable standards.
Organizations are not free to choose their level arbitrarily. The required CMMC level is dictated by contract requirements and the nature of the data involved. Understanding which level applies is a critical early step in any compliance effort.
CMMC Level 1 Overview
CMMC Level 1 focuses on the protection of FCI. It’s intended for organizations with limited exposure to sensitive data and establishes a baseline level of cybersecurity hygiene. At this level, organizations are expected to implement foundational safeguards that reduce the likelihood of common threats such as unauthorized access, data loss, or misuse.
Level 1 typically applies to organizations that do not handle CUI. Examples may include suppliers or service providers whose interaction with defense data is limited in scope. While Level 1 is often viewed as an entry point into the CMMC framework, it still requires intentional effort to ensure that basic practices are implemented consistently across systems and users.
One common Level 1 misconception is that “basic” means informal. We worked with a small supplier that technically had most of the required safeguards in place, but nothing was documented, and user practices varied widely. They passed internal checks repeatedly but failed their first readiness review because they could not demonstrate consistency. FCI was comingled with financials when they introduced a new financial system and leadership was unaware when exactly this happened. FCI does not stay where leadership thinks it stays. It follows the way work actually gets done. Level 1 is simpler, but it still requires intentional process and evidence.
Assessment expectations at Level 1 are simpler than at higher levels and do not involve a third-party audit. Organizations complete a self-assessment against the 15 Level 1 practices, submit the results to the Supplier Performance Risk System (SPRS), and annually self-attest that those practices are being performed. While the requirements are foundational, informal or ad hoc security habits often become visible once organizations are required to document and attest to what is happening.
For organizations looking to understand what readiness looks like at this level without diving into control-by-control detail, Cyberleaf provides additional guidance in CMMC Level 1 Ready in 30, which focuses on expectations and planning rather than technical configuration.
CMMC Level 2 Overview
CMMC Level 2 applies to organizations that handle CUI and represents a significant increase in scope, rigor, and operational impact. Level 2 aligns closely with NIST SP 800-171 and, in most cases, requires a third-party assessment conducted by an authorized C3PAO.
Organizations pursuing Level 2 compliance often underestimate the cumulative effort involved. While individual security controls may appear manageable in isolation, the overall burden of documentation, evidence collection, process consistency, and cross-functional coordination can be substantial. Compliance at this level is not achieved through technology alone.
Level 2 requires organizations to demonstrate that security practices are institutionalized. This means controls must be supported by documented policies, consistently followed by personnel, and reviewed over time. Leadership involvement, clear ownership, and coordination across IT, security, and business teams are all critical factors in achieving and maintaining compliance.
At Level 2, the gap between perception and reality grows. A 120-employee engineering firm we worked with believed they were “mostly compliant” because they had aligned to NIST 800-171 2 years earlier. They self-assessed at level 2 and were confident in their SPRS Score. What looked like a light validation effort turned into a broader operational rebuild. Closing the gaps took months, not weeks, and required participation from engineering, operations, HR, leadership, and IT. The issue was not that the organization had done nothing. It was that their compliance posture had not been maintained after they scaled up to meet a new contract for a prime and the business outpaced the levels required for a Level 2 assessment.
Cyberleaf explores these realities in Let’s Be Honest About CMMC Level 2: It Isn’t a Quick Process, which provides a grounded perspective on timelines, effort, and common pitfalls without duplicating implementation steps.
How CMMC Relates to Other Cybersecurity Frameworks
CMMC does not exist in isolation. For many defense contractors, confusion arises because CMMC intersects with cybersecurity standards and contractual requirements that have existed for years. Understanding how these frameworks relate to one another is essential for avoiding redundant effort and setting realistic expectations.
At its core, CMMC Level 2 is based on NIST SP 800-171, which is maintained by the National Institute of Standards and Technology. NIST 800-171 defines security requirements for protecting CUI in non-federal systems. Organizations that have previously aligned with NIST may already have a foundation in place, but alignment alone is not sufficient for CMMC.
CMMC introduces formal assessment and enforcement mechanisms that go beyond voluntary compliance. Where NIST alignment historically relied on self-attestation, CMMC requires organizations to demonstrate compliance through assessment. This distinction is critical. An organization may believe it is “NIST compliant” but still fail a CMMC assessment if documentation, evidence, or consistency expectations are not met.
CMMC is also closely connected to DFARS 252.204-7012, which governs the protection of CUI and mandates reporting of cyber incidents. DFARS requirements remain contractually binding regardless of CMMC status. In practice, CMMC reinforces and formalizes expectations that already exist within DFARS, rather than replacing them.
Some organizations ask whether certifications such as ISO 27001 can substitute for CMMC. While ISO 27001 can support broader information security governance and maturity, it does not replace CMMC requirements for Department of Defense contracts. CMMC is contract-driven compliance, and its requirements must be met regardless of other certifications an organization may hold.
Cyberleaf provides a deeper comparison of these frameworks in CMMC vs NIST 800-171: What Contractors Need to Know, which explores how organizations can align efforts without duplicating work.
Common Challenges Organizations Face With CMMC
Despite increasing awareness, organizations pursuing CMMC compliance consistently encounter similar challenges. These challenges are rarely limited to technology alone. More often, they stem from unclear scope, fragmented ownership, and misaligned expectations.
One of the most common issues is inaccurate scoping. Organizations frequently underestimate where CUI exists within their environment. CUI is often assumed to be limited to a specific system or department, when it may flow through email, file-sharing platforms, collaboration tools, or third-party applications. Late discovery of CUI expands compliance scope and increases remediation effort.
Another frequent challenge is tool sprawl. To move quickly, organizations may invest in multiple security tools without a clear strategy for how those tools support compliance. While security technology is important, tools alone do not create compliant processes or assessment-ready evidence. Over time, unmanaged tool sprawl can increase cost and complexity while still leaving gaps.
One organization believed they were “ahead of the curve” because they had invested heavily in security tooling. The best EDR/XDR, SIEM/SOAR coupled with automation and orchestration across the technology boundaries supported with all star incident responders. During readiness review, we found policies had not been updated in over three years, and evidence was scattered across shared drives with no clear ownership. Despite strong technology, documentation had been neglected and they were not assessment ready.
Documentation is another major stumbling block. CMMC assessments expect organizations to demonstrate not only that controls exist, but that they are implemented consistently and supported by documented policies and procedures. Organizations that rely on informal practices or tribal knowledge often struggle to produce the evidence assessors expect. CMMC requires control process like change management to be validation weekly, monthly, and annual review with leadership and SMEs. At Level 2, many organizations do not fail because they ignored compliance. They fail because they mistake old work for current readiness.
Finally, ownership and accountability issues can derail readiness efforts. When responsibility for CMMC is fragmented across IT, security, compliance, and leadership teams, progress slows and gaps persist. Successful organizations establish clear ownership and ensure leadership involvement early in the process.
Cyberleaf explores one of these issues in depth in Why Tool Sprawl Is One of the Biggest Barriers to CMMC Compliance.
What the CMMC Compliance Journey Looks Like
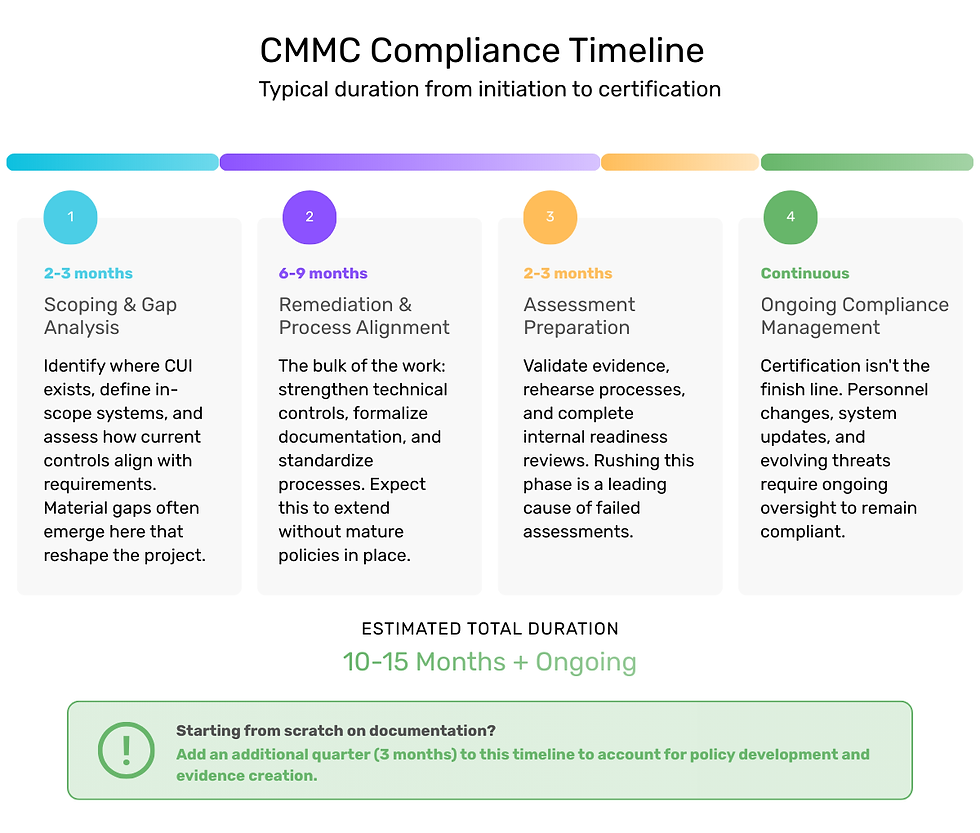
While every organization is different, most CMMC efforts follow a predictable timeline once scope and data flow are understood.
For a typical 100-person defense contractor pursuing CMMC Level 2
Scoping and gap analysis: 2–3 months
This phase identifies where CUI exists, which systems are in scope, and how current controls align with requirements. Many organizations uncover material gaps during this step that reshape the rest of the project.
Remediation and process alignment: 6–9 months
This is where most of the work occurs. Technical controls are strengthened, documentation is formalized, and processes are standardized. Organizations starting without mature policies or evidence should expect this phase to extend longer.
Assessment preparation: 2–3 months
Evidence is validated, processes are rehearsed, and internal readiness reviews are completed. Skipping or rushing this phase is one of the most common causes of failed assessments.
Ongoing compliance management: Continuous
Certification is not the finish line. Personnel changes, system updates, and evolving threats require ongoing oversight to remain compliant over time.
If you are starting from scratch on documentation, add an additional quarter to this timeline.
Cyberleaf provides additional perspective on this journey in How to Become CMMC Compliant: What to Expect, What to Avoid, and How to Get It Done.
Preparing for CMMC Without Disrupting Operations
A common concern among defense contractors is that CMMC compliance will disrupt normal business operations. In practice, disruption is most often caused by delayed preparation rather than the requirements themselves.
Organizations that wait until a contract mandates immediate compliance frequently face compressed timelines and rushed decisions. This reactive approach increases cost, stress, and the likelihood of mistakes. In contrast, organizations that begin preparing early gain flexibility.
Early preparation allows organizations to spread effort over time, align compliance initiatives with existing projects, and make informed decisions about scope and prioritization. It also enables leadership teams to balance compliance requirements with operational realities rather than treating CMMC as an emergency project.
Viewing CMMC as an operational maturity effort rather than a last-minute hurdle helps organizations integrate security into day-to-day processes. Over time, this approach reduces disruption and supports more sustainable compliance outcomes.
Choosing the Right CMMC Support Approach
CMMC compliance often involves a combination of internal resources, external advisors, and technology providers. Choosing the right approach requires understanding the role each component plays and how they fit together.
One issue we see repeatedly is conflict of interest. Many CMMC consultants also sell the security tools they recommend. That creates an incentive to over scope environments, push unnecessary platforms, and inflate long-term costs.
We believe advisory and product sales should be separate. CMMC readiness should be driven by scope, data flow, and contractual requirements, not by what someone happens to resell. Organizations benefit when guidance is architecture-agnostic and focused on assessment success rather than tool adoption.
It is also important to consider long-term support. Achieving certification is only part of the journey. Maintaining compliance over time requires ongoing attention, and organizations should ensure that any support approach extends beyond initial assessment.
Cyberleaf approaches CMMC with an advisory-first mindset, helping organizations navigate complexity while aligning security efforts with business objectives. More information about this approach is available on the Cyberleaf CMMC Advisory Services page.
What Most Contractors Get Wrong About CMMC
After working with organizations across multiple industries and assessment stages, we see the same mistakes repeated again and again.
Buying infrastructure before scoping
Many contractors commit to GCC High or expensive enclave architectures before fully understanding where CUI actually lives. That can be a five-figure decision that turns out to be unnecessary once scope is properly defined.
Assuming tools equal compliance
Security platforms help, but they do not create compliant processes. We regularly encounter organizations with strong toolsets that still fail readiness checks because policies, evidence, and consistency are missing.
Assuming your MSP understands CMMC
Many MSPs are strong at general IT support, but CMMC requires more than keeping systems running. We routinely see providers struggling to translate IT support into CMMC expertise, especially when scoping, CUI boundaries, evidence, and assessment defensibility are on the line.
Treating CMMC as an IT project
CMMC is an organizational change effort. When ownership is isolated to IT without leadership involvement, progress stalls and gaps persist.
One of the biggest risks in CMMC preparation is assuming your organization already knows what “compliant” looks like. Many organizations and their providers can manage tools and infrastructure, but far fewer understand how to design, document, and defend an environment against CMMC Level 2 expectations.
Organizations that avoid these pitfalls typically spend less, move faster, and experience fewer surprises during assessment.
CMMC Resources and Next Steps
CMMC compliance can feel overwhelming, particularly for organizations encountering the framework for the first time. Clarity improves when organizations focus on understanding scope, expectations, and the overall journey before diving into implementation details.
Cyberleaf maintains a growing library of CMMC-focused blogs, checklists, and webinars designed to support organizations at every stage of the compliance journey. These resources provide deeper insight into specific topics without duplicating content on this page.
If you aren’t sure where your organization stands today or what steps make sense next, these resources offer a strong starting point. For organizations seeking tailored guidance, a CMMC readiness conversation can help clarify priorities, identify risks, and reduce uncertainty.

-1.png?width=520&height=294&name=HubSpot%20Blog%20Images%20(15)-1.png)
.png?width=95&height=125&name=Threat%20Report%20(1).png)